The use of the cloud is set to grow exponentially throughout 2022. The Cloud Configuration Security Practices survey conducted by Cyber Security Hub found that as of November 2021 enterprise companies in sectors that include financial services, healthcare and communications have on average 29 applications deployed in the cloud, which is set to grow to closer to 144 applications over the next 12 months. This represents a 395 percent increase.
As cyber threats evolve and cloud application adoption accelerates, organizations must ensure their security practices are keeping up.
Cloud delivery is self-service but security is not

Of those surveyed in Cyber Security Hub’s Cloud Configuration Security Practices survey, an average of 68 percent said their organization’s infrastructure services (i.e., computer, storage or databases) are provisioned using Infrastructure-as-Code (IaC) or similar software defined tools.
IaC is the process of managing and provisioning data centers through code, rather than manually.
Provisioning cloud services through IaC saves both time and money. It minimizes human error and reduces the reuse of gold masters. Moreover, every change that is made is documented, meaning there is full accountability and traceability of configuration changes.
Cloud is delivered as code but security is not
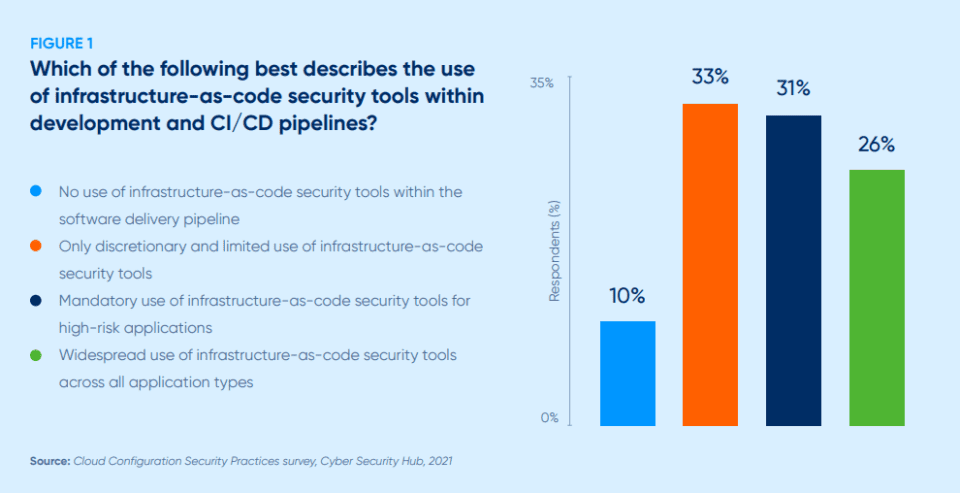
The Cloud Configuration Security Practices survey shows there is a mixed approach to how and when security tools are being used. A total of 74 percent of respondents said that their pipelines are not using IaC security tools widely across their cloud applications portfolios.
Widespread IaC security tools across all application types were only found in 26 percent of respondents. While IaC security tools are being used in either a discretionary/limited way (33 percent) or are mandatory for high-risk applications (31 percent) there is not yet widespread use of these security tools (see Figure 1).
Bradley J. Schaufenbuel, VP and CISO at Paychex, says that the HR and payroll solutions firm had recently performed extensive evaluation of IaC security tools, but the company has not yet purchased one. IaC security tools identify vulnerabilities in IaC scripts such as embedded plaintext passwords and keys.
Organizations are failing to respond fast enough

A fast response to security issues is required in any setting beyond the realm of cloud applications. The survey found that it takes more than 70 percent of organizations more than one week to detect and remediate a single cloud services risk.
The results show that 70 percent of respondents said it takes more than 24 hours to detect a violation within a cloud service; 72 percent said it takes more than 24 hours to identify the application causing the violation; 75 percent said it takes more than 24 hours to assign the issue to a developer for remediation; 80 percent said it takes more than 24 hours to correct the violation; and, finally, 72 percent said it takes more than 24 hours to verify the fix (see Figure 2).
One issue that is prevalent is that security teams are stretched, under resourced and dealing with a large number of security issues on a regular basis. In addition, because traditional cybersecurity is not being delivered as code it is not, therefore, able to keep pace with cloud self-service delivery.
Shifting cloud security left is imperative

Runtime detection and response are a must for securing cloud environments, but the cloud is so big and moves far too fast for organizations to exclusively pursue a reactive cyber security strategy. The number of security tickets continues to pile up as is evident by the results of our survey.
The Cloud Configuration Security Practices survey found that on average 62 percent of respondents are concurrently managing hundreds or more tickets specific to cloud misconfiguration, with almost one-third managing thousands to tens of thousands of tickets (see Figure 3).
With risk levels high, when using public cloud infrastructure organizations must be extremely confident in their ability to stop a cloud breach that could expose their critical data, or take critical services offline.
Shifting cloud security left is imperative

The survey also showed that 79 percent of respondents said they were less than extremely confident that their runtime security tools were sufficient to keep their cloud data and workloads safe (see Figure 4).
Runtime tools are able to find and detect risks in the wild that actively expose organizations to incidents and breaches. However, in runtime it is a race to find and fix threats before bad actors exploit them. In addition, false negatives and false positives can be an issue with runtime tools leading to alert fatigue which poses a big challenge with regards to an organization’s ability to respond quickly.
Those that are using IaC security tools are doing so in varying ways: alert-only to IaC violations and exposures, based on pre-established security policy guardrails, risky code is allowed to proceed to production (29 percent each); to prevent code release to production due to infrastructure-as-code violations and exposures, based on preestablished security policy gates where remediation is performed manually (30 percent); and finally automatic remediation of infrastructure-as-code violations and exposures, based on pre-established security policy guardrails and gates (29 percent).
Security automation is crucial to cloud innovation

Automating processes is key to maintaining efficiency across a multitude of business practices beyond the realm of cyber security and cloud computing.
With over 70 percent of organizations saying it takes them more than one week to find and fix a single cloud security risk automation becomes a necessary tool for security teams to keep pace with cloud application delivery.
Of those surveyed, 80 percent of organizations said it takes more than 24-hours to perform a manual review of a single cloud application’s infrastructure-as-code, of which 47 percent take more than one week (see Figure 5).
Automated testing is exponentially faster than manual processing and Schaufenbuel notes that it also tends to be more accurate, as human error within manual security reviews can result in missed vulnerabilities.
Security automation is crucial to cloud innovation
Manual deployment, lack of skills and diminished manpower were all highlighted as challenges to deploying a cloud service by those responding to the survey.
Security reviews remain a bottleneck to migrating cloud applications to public cloud safely. One in two survey respondents said that on average their security teams can perform up to three cloud application security reviews per week.
Many survey respondents said that they do not have full confidence that cloud security requirements are being implemented correctly and consistently. With the exponential increase in cloud applications that are expected, many security teams will simply be unable to keep up with the pace.
Conclusion
The results of our survey show that there is a huge amount of cloud adoption ongoing with many organizations set to increase the number of applications in the cloud in the near future. There remain, however, a large number of security gaps and challenges. Many are using IaC security tools in a limited capacity, but the scope of usage is far from ideal, leaving organizations blind to security threats that pose a high risk of incident or breach.
There is clearly a need for organizations to implement cloud security in a manner consistent with how they provision public cloud services – in code.
For innovation to continue on an upward trajectory cloud security must keep pace with cloud development and delivery. Otherwise, businesses will have to either throttle back cloud innovation or blindly accept the risks of moving applications to public cloud.
With security-as-code, companies are enabled to achieve the same level of self-service for governing and securing public cloud that they have with the development and use of the cloud itself.
How is your company implementing cloud security? Let us know in the comments
originally published onhttps://www.cshub.com/cloud/articles/the-state-of-cloud-configuration-security-practices-2